
As we increasingly rely on technology for our daily lives, it's more important than ever to be aware of the dangers that come with it. One of the biggest threats online is phishing scams – fraudulent attempts to steal sensitive information like passwords or credit card numbers. Whether through a fake email or a convincing copycat website, these scams can be difficult to spot. That's where this guide comes in.
With over 65 facts and statistics, we'll walk you through everything you need to know to avoid falling victim to this crime, as well as an overview of the state of phishing in 2024. From identifying the signs of a scam to simple but effective preventative tools, this comprehensive guide will give you the tools and information you need to protect yourself online.

What Is Phishing?
Before you can protect against an attack, it helps to understand exactly what phishing is and recognize the signs that someone might be targeting you.
Phishing is a cybercrime.
The scammer contacts its targets by email, phone call, or text, pretending to be a legitimate organization and asking for sensitive information. This initial communication is sometimes known as “bait.”
These emails, phone calls, or texts may look noticeably suspicious, or be difficult to distinguish from the real thing.
Signs of phishing:
The sender is someone you don’t know.
They might claim to be from a legitimate organization, but their email address would suggest otherwise (for example, it might have spelling errors or be a random selection of letters and numbers).
Look for unusual links.
It’s not just email addresses that may seem a bit off — look for unusual links, too. They may appear normal at first glance, but if you look closer, there might be missing or incorrect letters in the spelling of a popular website, or the domain may end in .biz instead of .com.
Some phishing scams may include attachments in the emails or texts.
These normally contain viruses or malicious programs, so avoid clicking on them.
The sender urges you to act quickly.
For example, they might say that you only have a limited amount of time to share your information before they close your account. Legitimate organizations never make these kinds of ultimatums.
The sender is offering you something that sounds too good to be true.
It might be an all-expenses-paid holiday, a free phone, or a large sum of money. Unfortunately, even though you know it’s improbable, you may be tempted to click through just in case.
Cybercriminals may ask for your bank details, passwords, or other information that allows you to be personally identified.
Remember that a genuine email from a bank:
- Will be from an authentic email address (you can check with your bank if you’re unsure)
- Won’t ask you to confirm your banking password
- Won’t ask you to confirm your bank card details
- Won’t ask you to confirm your security answers
Once acquired, personal information can be used to access your accounts and carry out fraudulent activity.
Cybercriminals may spend your money or pose as you to open new accounts.
Research published in 2021 found that the most commonly used words in phishing emails are:
Urgent
(8%)
Request
(5.8%)
Important
(5.4%)
Payment
(5.2%)
Attention
(4.4%)
The same research found that scammers used the following reasons as excuses to send phishing emails:
Bills or invoices
(15.7%)
Email delivery failures
(13.3%)
Package deliveries
(2.4%)
Additionally, the same analysis found that of the sample of phishing emails studied:
- 54% were from male senders
- 38% were from female senders
- 8% were from an unknown sender
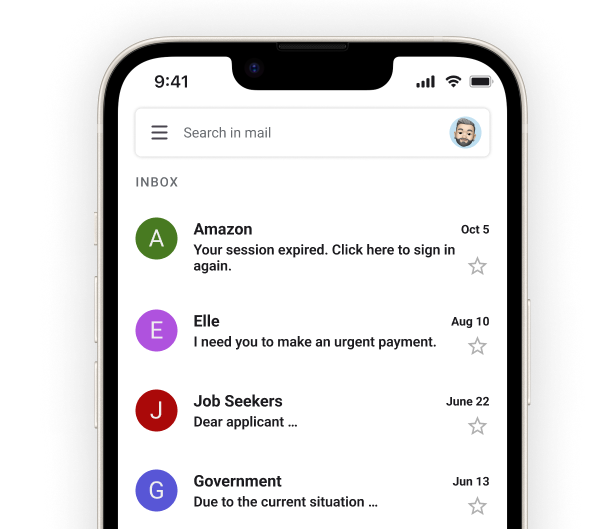
Scammers often use the email subject line to get the attention of the recipient. Some of the most common subject lines in phishing emails include:
- Your session expired. Click here to sign in again.
- I need you to make an urgent payment.
- Dear applicant …
- Due to the current situation …
- Merry Christmas!
- We are unable to process your tax return.
- No response required.
Phishing attacks are used as a starting point for other cyberattacks.
Emails, in particular, are used as a way to deliver ransomware, which prevents you from being able to access your device and its data. The attacker will ask for a ransom before they give you access again.
Phishing is the most commonly used and widely known name for this type of cybercrime.
However, text phishing is sometimes known as “smishing” (aka SMS phishing), and voice phishing (over the phone) is sometimes known as “vishing.”
Cybercriminals may also attempt spear phishing.
Spear phishing occurs when the scammer already has some information about the person they’re targeting. They use this to make their emails seem more authentic.
A type of spear phishing called “whaling” targets high-ranking employees at organizations.
Cybercriminals will try to gain sensitive information that can affect their performance and reputation.

The Beginning of Phishing
Tim Berners-Lee created the World Wide Web in 1990, and the first browsers followed in the next couple of years, with internet use exploding over the 1990s. However, with this innovation came opportunities for cybercriminals to establish scams.
The first phishing attacks are thought to have started in the mid-1990s.
A group of cybercriminals posed as AOL employees and used instant messaging to persuade users to share personal details like passwords. The term “phishing” was coined in 1996.
Scammers began registering similar domain names to legitimate brands in 2003.
They would then email customers asking them to update their details on the fake sites, gaining a plethora of personal information (including credit card details).
The first phishing lawsuit was filed in 2004.
The Federal Trade Commission (FTC) filed against a 17-year-old boy from California who’d created a fake AOL website.

How Widespread Is Phishing?
Phishing scams are one of the most common threats facing internet users today, and they’re carried out across the world.
Approximately 3.4 billion spam emails are sent every day.
This is equal to 102 billion per month (if we define a month as 30 days) or over 1 trillion per year. These are significant numbers, given that the world’s population is over 8 billion. Many of us will receive a phishing email at some point.
90% of cyberattacks start with phishing emails.
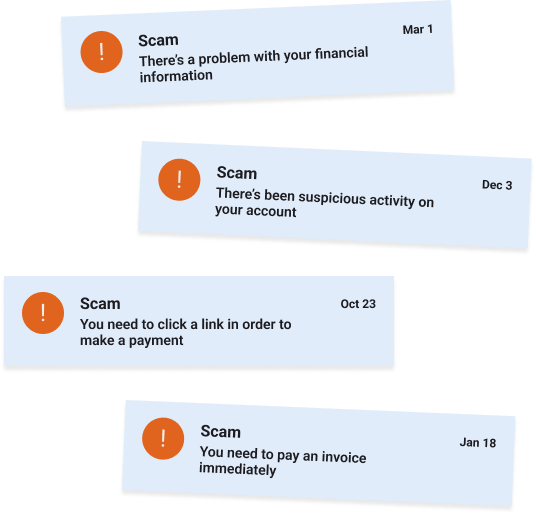
By telling a story the user might believe to be true, these emails can persuade recipients to share their details — or perhaps be scared into doing so. Some of the stories cyberattackers tell:
- There’s a problem with your account information
- There’s a problem with your financial information
- You need to confirm your account information
- You need to confirm your financial information
- There’s been suspicious activity on your account
- You need to pay an invoice
- You need to click a link in order to make a payment
- You need to register with a particular plan in order to get a refund
- You’ve won something
Google blocks approximately 15 billion unwanted emails every day.
It uses a mixture of AI and rule-based filters, with the AI looking for new patterns as phishing styles change.
The most popular email accounts across the world are Apple (58.08%), Gmail (29.68%), and Microsoft Outlook (4.04%), with Gmail thought to be particularly popular with scammers.
This could be because of Google’s good reputation, the ease with which you can set up a Gmail account, and the fact Gmail gives you the option to turn on read receipts. Even if they don’t get a reply, spammers will know whether or not someone has seen their bait email.
In 2023, 45.6% of all emails were spam, down from 48% in 2022.
The number of phishing sites reached a high in Q1 of 2023, at over 1.6 million.
By Q2 of 2023 this had dropped to just under 1.3 million.
Americans lost $10.02 billion to scams in 2023.
Scammers often pretended to be from banks or other financial institutions to gain access to people’s accounts and money.
Interestingly, the U.S. is the country with the most blocked URLs, although not all of these may be related to links in phishing emails.
The full list of countries is as follows:
U.S.
(20.5%)
Germany
(9%)
Italy
(8.6%)
Japan
(5.4%)
Brazil
(4.4%)
U.K.
(5.2%)
Colombia
(4.3%)
France
(3.4%)
Canada
(3.3%)
Singapore
(2.8%)
The most recent cybercrime report from the Internet Crime Complaint Center (IC3) notes that it received 880,418 complaints from the American public in 2023.
This was an increase of 10% compared to the previous year.
Financial losses increased significantly year-on-year, from $10.3 billion in 2022 to over $12.5 billion in 2023.
This was a 22% increase.
The same report shows that phishing was the cybercrime with the most victims in 2023, although the number is down slightly compared to 2022.
There were 298,878 phishing victims in the U.S., with a significant gap between this figure and the next cybercrime on the list: personal data breach (55,851 victims in the U.S.).
The IC3 currently has a 71% success rate in recovering or freezing funds.

Recent Phishing Trends
As time goes on, cybercriminals become increasingly sophisticated in their methods of attack. Whereas their phishing communications once had very clunky presentation, with strange syntax, misspelled words, and odd greetings, nowadays, they are more likely to make an effort to pretend things are legitimate. There are also more ways they can carry out a phishing attack, as we have far more ways to communicate than we used to. Here are some phishing trends to look out for in 2024 and beyond.
Phishing attacks are becoming more sophisticated, but the overall level of spam is decreasing.
45.6% of emails were considered spam in 2023, down from 48.63% in 2022.
The most impersonated industry in 2023 was financial institutions, at 42.1%.
Social media
(26.1%)
Webmail and online services
(11.4%)
Telecommunications
(8.3%)
Cloud storage and file hosting services
(5%)
In the first quarter of 2024, 51.3% of phishing website URLs ended in .com. This was followed by:
.org
(4.7%)
.us
(2.4%)
.co
(2.3%)
Cybercriminals have turned to LinkedIn.
It may not be the first social media platform you think of, but it offers ample opportunities for scammers, as there are over 1 billion users worldwide as of 2024. Attackers may target people who have recently changed their job, posing as staff at the new company to gain personal information.
It’s not just employees whom attackers might impersonate, but also brands themselves.
This is a type of phishing that’s sometimes referred to as “spoofing.” Globally, the brands used most often in spoofing attempts are:
- Walmart (39%)
- Microsoft (14%)
- Wells Fargo (8%)
- Google (4%)
- Amazon (4%)
PayPal is the most frequently impersonated payment system in phishing attacks by a long margin at 84.23%. The other most impersonated systems are:
MasterCard
(3.75%)
Visa
(3.1%)
American Express
(2.02%)
Acxsys
(1.9%)
Cielo S.A.
(1.33%)
square
(0.76%)
Japan Credit Bureau
(0.72%)
UC Card Co. Ltd
(0.43%)
The cost of cybercrime has increased over recent years.
It’s expected to reach $10.5 trillion by 2025. These costs are often the result of money being stolen through fraud.
Many phishing attacks are carried out over email.
However, IT professionals have noticed an increased variety of delivery methods, particularly since the pandemic changed how we’re likely to communicate. Delivery methods that have notably increased include:
Video conferencing platforms
(44% increase)
Workforce messaging platforms
(40% increase)
Cloud-based file-sharing platforms
(40% increase)
SMS
(36% increase)
95% of cybersecurity leaders are stressed about email security.
There’s also been an increase in phishing attacks via social media, particularly on businesses, although the momentum of these slowed towards the end of 2023.
The average business experienced 83 attacks in January 2023, but 57 in December 2023.
Brand impersonation was the biggest threat in Q4 2023, at 45% of cases
53.93% of reported social media attacks in Q4 2023 were aimed at the banking industry.
Other targeted industries include:
- Financial services (26.38%)
- Retail (5.32%)
- Credit unions (2.88%)
- Payment services (2.01%)
- Technology (1.95%)
AI has become a much-discussed topic over the last year or so, especially with the introduction of ChatGPT in late 2022.
And AI is having an impact on phishing. Scammers can use AI programs to write phishing emails that look legitimate without the spelling, grammar, or syntax errors that so often characterized earlier scam communications. Cybersecurity experts have expressed concern that the number of successful phishing attacks will rise.
AI can also be used specifically for spear phishing, in which personal information relevant to the recipient is used to sound more legitimate.
Scammers now use AI to take personal information from data breaches and create mass spear phishing attacks.
It’s not just emails that AI is impacting — phishing calls (also known as “vishing”) are being updated, too.
AI can take a clip of someone speaking and replicate the sound of their voice, convincing those who know them to share personal information that scammers can use for fraudulent purposes.

How Many People Fall Victim to Phishing?
With phishing being so widespread, it’s perhaps not surprising that so many people have been affected by it, both in the U.S. and further afield.
Recent statistics by Forbes have revealed that in 2022, there were 300,497 victims of phishing in the U.S. alone, with a total loss of $52,089,159 between them.
The same statistics show that across the U.S.:
Nevada
is the state most affected by phishing scams, while Kansas is the least affected.
Arkansas
lost the most money through phishing scams: over $80,000 per 100,000 residents.
Delaware
has seen the largest increase in phishing scams since 2018, at 71%.
Wisconsin
has seen the largest increase in phishing scam victims since 2018, at 38%.
Forbes found that the following 20 states were the most and least affected by phishing scams:
Scroll right to view →
| Most Affected | Least Affected | |
|---|---|---|
| 1 | Nevada | Kansas |
| 2 | District of Columbia | Mississippi |
| 3 | New Jersey | Iowa |
| 4 | California | Idaho |
| 5 | New York | Alabama |
| 6 | Florida | Maine |
| 7 | New Hampshire | South Carolina |
| 8 | Washington | West Virginia |
| 9 | Illinois | South Dakota |
| 10 | Wyoming | Pennsylvania |
Forbes also found that the following 20 states experienced the highest and lowest financial losses caused by phishing scams:
Scroll right to view →
| Highest Financial Losses (Rounded to the Nearest Whole Number) |
Lowest Financial Losses
(Rounded to the Nearest Whole Number) |
|||
|---|---|---|---|---|
| 1 | Arkansas | $80,318 | Delaware | $139 |
| 2 | New Hampshire | $47,477 | Kansas | $294 |
| 3 | Nevada | $37,478 | Maine | $384 |
| 4 | California | $37,281 | Idaho | $983 |
| 5 | Montana | $31,993 | Iowa | $1,150 |
| 6 | New Jersey | $30,779 | Alabama | $1,172 |
| 7 | Utah | $28,758 | Mississippi | $1,242 |
| 8 | Connecticut | $26,093 | South Carolina | $1,355 |
| 9 | District of Columbia | $25,562 | Indiana | $1,682 |
| 10 | North Dakota | $24,010 | Maryland | $1,857 |
Worldwide, there are thought to be 1.35 million unique phishing sites.
Vietnam is the country most targeted by phishing attacks.
The average cost of a data breach for an organization is $4.45 million, according to IBM’s latest data breach report.
This is up from $4.35 million the previous year, a 2.3% increase.
The high cost can be attributed to several factors:
- Users/customers are unable to access the website, product, or service
- The breach can damage the company’s reputation, causing customers to look elsewhere
- Companies can lose intellectual property
- Companies can lose money taken by the cybercriminals
- Companies may receive a fine
- Fixing and improving cybersecurity can have a significant cost
- Companies may have to pay legal fees
The same report found that the industries with the most expensive data breach costs were:
- Healthcare ($10.93m)
- Financials ($5.9m)
- Pharmaceuticals ($4.82m)
- Energy ($4.78m)
- Industrial ($4.73m)
Of the brands impersonated in phishing emails in the last quarter of 2023, Microsoft was the most impersonated ( 33% of attempts).
They were followed by Amazon (9%) and Google (8%).
Amongst employees who’ve fallen for a phishing attack:

How can you prevent phishing?
We’ve covered some of the more obvious signs of phishing. However, prevention is better than cure, so here are some ways to protect yourself as an individual or protect an organization.
Use a spam filter for your email inbox.
Although not effective 100% of the time, a spam filter keeps most unwanted emails out of your inbox. Each one is slightly different as they’re based on a set of guidelines that determine whether or not an email is legitimate. You may need to check your spam folder occasionally in case a legitimate email is sent there.
There are 5 types of email spam filters:
Blacklist filter
Removes emails from suspicious domains or those that come from senders who have been marked as spam by multiple users.
Content filter
Looks for words and information often used in spam emails.
Header filter
Focuses on the recipient, sender, and subject to determine whether an email is likely to be spam.
Language filter
Removes any emails that aren’t in the recipient’s email inbox language.
Rule-based filter
A set of rules are followed and any emails that don’t meet the criteria for a legitimate email are sent to the spam folder.
Google unknown numbers that try to call or message you.
People often report suspicious numbers online, which will give you an idea of whether or not the caller is legitimate. Block any numbers which are likely to belong to spammers.
Install the most current version of your web browser.
Browsers are updated in response to the latest cybersecurity threats, so you’re more protected using the most recent version. You can also find security information for some of the most common browsers here:
Use multi-factor authentication.
As well as a password, you’ll need a one-time verification code, normally sent by text or email. Even if a phishing attempt successfully gets your password, scammers may not be able to log in if they don’t have access to your phone. Many platforms will notify you of suspicious activity, allowing you to update your password and strengthen your security.
For businesses, employee education is crucial to their defense against phishing attacks.
84% of U.S.-based organizations reported that cybersecurity awareness training reduced how often employees fell for phishing scams. Knowing the signs can make someone think twice and report emails they’re unsure of.
Worryingly, the 2023 State of the Phish report found that many respondents had trouble defining key cybersecurity threats, with 42% unable to define ‘phishing’.
The same report found that only 56% of global organizations with cybersecurity training programs train their entire workforce
Only 35% carried out phishing simulations to see if employees reported suspicious activity.
Just under 20% of organizations only provide annual phishing awareness training, while 33% don’t provide any training to remote employees — despite 74% of them having access to critical data.
This is arguably not enough, given how quickly the cybersecurity landscape can change and how devastating an attack can be.
It takes an organization 197 days to discover a data breach and up to 69 days to contain it, according to a report by IBM.
Signs of a data breach include:
Changes to files
Keep track of who changes files, when, and why. Any unexplainable changes could be the result of a breach.
Unusual account activity
This includes employees being locked out of their accounts. This often happens when the scammer poses as a fellow employee through a phishing scam and asks for personal information like passwords.
Slow devices and networks
Malware can cause these not to function as they should. The IT department will be able to identify what could be causing the slowdown, and antivirus software can also help.
Pop-ups
An increase in pop-ups or devices crashing without explanation.
Use a secure email gateway (SEG).
A SEG monitors all emails going to and from employees’ accounts, blocking anything it deems suspicious before it reaches the recipient. SEGs aren’t a failsafe, as some scammers can mimic legitimate senders, but they offer an extra layer of security.

What if I Fall Victim to a Phishing Attack?
With scams becoming smarter, sometimes you can take all precautions and still encounter a phishing attack. Here are the steps to take if you think you’ve been targeted.
Change your passwords from a different device.
Ensure they’re a mix of numbers, letters, and symbols, and don’t use any of the most common passwords (like “qwerty”, “password” or “123456”). Use a secure password manager so you don’t have to worry about remembering them.
Set up 2-factor authentication.
This extra step means it’s more difficult for an outsider to access your accounts.
Disable your internet connection.
This will stop any viruses from spreading to other devices.
Reach out to your bank.
Let them know your financial information may have been accessed in a phishing attack. They may send you a new card or freeze your account. If the account remains active, check it frequently for any suspicious activity.
Contact a credit reporting agency.
This is especially important if you’ve given away personal information due to the phishing attack. They’ll let you know if you need to place a fraud alert on your file. The numbers you need to call are:
Run a scan on your device.
Reputable antivirus software should be able to detect signs of malware or a data breach.
Back up your files to an external hard drive.
This protects you against losing any important documents if your device becomes infected.
If a brand was impersonated (“spoofed”), let them know as soon as possible.
They’ll be able to reach out to their customers to inform them of the scam and prevent others from falling victim to it, too.
Report the attack.
You can do so by:
Giving the sender’s details to the
Reporting it to the
Reporting it to the
Phishing attacks remain a major risk to everyone in the online world. As we’ve seen, the consequences of a phishing attack are real and can be devastating for those who lack sufficient awareness or protection measures.
Be proactive by following the advice mentioned here. Increasing your cybersecurity, along with a healthy dose of skepticism when interacting with communication from unknown sources, will help protect you. With vigilance, you can ensure that your valuable data remains secure online.
